We are living in the age of information overload, but perhaps more accurately, we are living in the age of the “Inbox Siege.” You know the feeling: you sign up for a single 10% discount coupon at a clothing store, or you download a whitepaper for work, or you connect to the free Wi-Fi at the airport. It seems like a harmless transaction—your email address for their service.
But within days, the trickle begins. First, it’s a “Welcome” email. Then, a newsletter you didn’t realize you opted into. Then, the partner offers. Suddenly, your primary inbox, the digital hub of your life where you receive bills, family photos, and work correspondence, is buried under a mountain of unsolicited junk.
Spam is not just a nuisance; it is a security risk. Every time you hand out your primary email address, you are handing out a piece of your digital identity. If that company suffers a data breach (a question of when, not if), your email is sold on the dark web, leading to phishing attempts, credential stuffing attacks, and an avalanche of robomails.
The solution to this modern plague is not to stop using the internet, nor is it to spend hours every week unsubscribing. The solution is to stop giving out your real address.
Enter the Temporary Email Address (also known as a disposable or “burner” email).
Using a temporary email is the digital equivalent of wearing a mask. It allows you to participate in the online world without leaving a permanent footprint. It keeps your primary inbox pristine and your digital identity secure. This comprehensive guide will teach you the mechanics, the strategies, and the best tools for using temporary emails to reclaim your digital peace of mind.
The Economy of Spam: Why Your Inbox is a Target
To understand why temporary emails are necessary, we must first understand the enemy. Why is your email address so valuable?
In the digital economy, data is the new oil, and your email address is the drill site. It is a unique identifier that links your online behaviors. Marketers use it to track you across platforms. Data brokers scrape it to build profiles on your purchasing habits, political leanings, and financial status.
When you enter your email into a form, three things often happen:
- The Direct Sale: The company uses it to market to you directly.
- The Affiliate Share: The company shares your data with “partners” (a clause usually buried in the Terms of Service).
- The Breach: The company stores your email insecurely. Hackers steal the database and sell it to spammers.
Once your email is on a “verified active” list, it is nearly impossible to get it off. Unsubscribing can sometimes make it worse, as it confirms to the spammer that there is a human on the other end of the line. The only foolproof defense is to ensure they never had your real address in the first place.
What is a Temporary Email Address?
A temporary email address is a fully functional email account that is designed to be short-lived. It allows you to receive mail (and sometimes send it) for a specific period—ranging from 10 minutes to a few months—before self-destructing or being deleted by the user.
It allows you to:
- Receive the verification link required to sign up for a site.
- Download the content or access the service.
- Abandon the address immediately.
There are generally two categories of temporary emails, and knowing the difference is critical for your data safety.
The “Burner” (True Disposable)
These are ephemeral accounts. You visit a website, it generates a random address (e.g., x9s7f@tempmail.com), and the inbox is live immediately in your browser. You do not need to create a password or log in. Once you close the tab or a timer runs out, that email address and all its contents are deleted forever.
The “Alias” (Forwarding Mask)
This is a more sophisticated approach. Services like Apple’s “Hide My Email,” Firefox Relay, or SimpleLogin create a fake email address that forwards messages to your real inbox. If one of these aliases begins receiving spam, you can simply toggle a switch to “block” that specific alias. This allows you to maintain a long-term account with a service without revealing your true email.
When to Use a Temporary Email (The Green Zone)
You should use a disposable address whenever the trust level of the entity asking for it is low or the value of the transaction is temporary.
One-Time Downloads and Gated Content
Marketers often “gate” valuable content like eBooks, PDF guides, or software trials behind an email wall. If you only need the file and have no interest in their newsletter, use a burner email.
Public Wi-Fi Access
Airports, coffee shops, and hotels often require an email address to access their free Wi-Fi. This is purely a data harvesting tactic. Use a temporary email to connect without ending up on a mailing list for a hotel chain you will never visit again.
Online Shopping Coupons
Many retail sites offer a “15% off your first order” code if you sign up for their newsletter. You can use a temporary email (or an alias) to get the code. If you want to use the coupon again later, you can use a new temporary email to be a “new customer” again.
Untrusted Forums and Comment Sections
If you want to leave a comment on a blog or join a discussion forum that requires registration, but you don’t plan on becoming a long-term community member, protect your identity with a disposable address.
Testing Apps and QA
For developers or curious users who want to test the onboarding flow of an app without cluttering their main account, burner emails are essential tools.
When NEVER to Use a Temporary Email (The Red Zone)
While powerful, temporary emails have a fatal flaw: impermanence. If you lose access to the email address, you lose the ability to reset your password for any account linked to it. Never use a burner email for:
- Banking and Finance: Your credit card, PayPal, and bank accounts must be linked to a secure, permanent email address.
- Healthcare Portals: Medical records require secure, permanent access.
- Government Services: Taxes, voting registration, and vehicle licensing.
- Primary Social Media: If you care about your main Facebook, Twitter, or Instagram account, do not use a disposable email. If you get locked out for a security check, you will never get back in.
- Job Applications: You want recruiters to be able to find you.
How to Use “Burner” Services: A Step-by-Step Guide
For quick, one-off interactions, “Burner” sites are the fastest solution. Here is how to navigate them effectively.
Popular Services
- 10 Minute Mail: The classic. It gives you an address that expires in 10 minutes (with an option to extend).
- Guerrilla Mail: Offers an address that lasts for one hour. It also allows you to send mail, which is rare for these services.
- Temp Mail: Offers a clean interface and a mobile app for on-the-go generation.
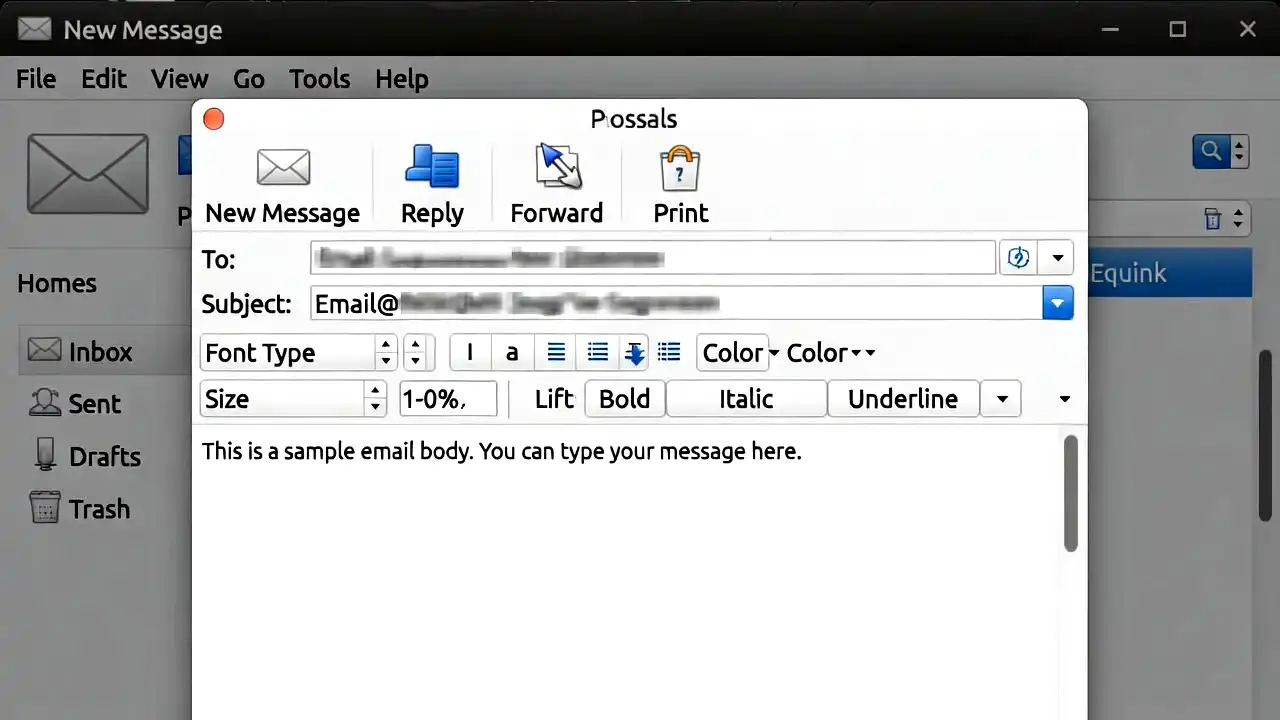
The Workflow
- Open the Service: Navigate to the website (e.g., 10minutemail.com).
- Copy the Address: The site will automatically generate an address for you. Click the “Copy to Clipboard” button. Do not close this tab.
- Register: Go to the website you want to access and paste the burner email into the registration field.
- Wait for the Ping: Switch back to the burner email tab. Wait for the verification email to appear in the browser inbox.
- Verify: Click the verification link inside the email.
- Close: Once you have accessed the content or service, close the burner tab. The email address will vanish into the digital ether.
Warning: Do not use the same browser window for the burner email and the service you are signing up for if you are concerned about tracking cookies. Use “Incognito” or “Private” mode for the burner site to ensure total separation.
The Advanced Method: Email Aliasing for Long-Term Control
The “Burner” method is great for quick hits, but what if you want to sign up for a newsletter you actually might want to read, but you want the option to kill it if it gets annoying? Or what if you want to sign up for Netflix but don’t want Netflix to have your real email?
This is where Email Aliasing (Masking) comes in. This is the professional standard for spam reduction.
How Aliasing Works
An aliasing service acts as a middleman.
- You create an alias (e.g., netflix.watch324@simplelogin.com).
- You give this alias to Netflix.
- Netflix sends an email to the alias.
- The aliasing service forwards the email to your real inbox (real.name@gmail.com).
- If Netflix starts spamming you, or if they get hacked and spammers start using that alias, you simply toggle the alias “Off” in your dashboard. The spam stops instantly, and your real inbox remains secure.
Top Aliasing Tools
The top and effective aliasing tools you may consider.
Apple “Hide My Email”
If you are in the Apple ecosystem (iCloud+ subscriber), this is built in.
- How to use: Whenever you tap on an email field in Safari or an app, iOS will suggest “Hide My Email.” It instantly generates a unique @icloud.com address that forwards to you. You can manage and delete these in your iCloud settings.
Firefox Relay
Mozilla, the maker of the Firefox browser, offers a privacy-centric relay service.
- How to use: Install the extension. It adds a button to email fields that generates a mask ending in @mozmail.com. The free tier offers a limited number of masks; the paid tier is unlimited.
SimpleLogin / AnonAddy
These are power-user tools (SimpleLogin is now owned by Proton). They are open-source and highly customizable.
- Benefits: They allow you to reply anonymously. If you reply to a forwarded email, the service strips your real address and sends the reply from the alias, maintaining your privacy during a two-way conversation.
The “Plus Addressing” Trick (The Poor Man’s Alias)
If you use Gmail, Outlook, or Proton Mail, you can use “plus addressing.”
- The Trick: If your email is name@gmail.com, you can sign up as name+newsletter@gmail.com or name+gym@gmail.com. The email will still arrive in your main inbox.
- The Pro: It helps you filter emails. You can set a rule that says, “If sent to name+gym, move to folder X.” It also tells you who sold your data. If you start getting mortgage spam at name+gym, you know the gym sold your list.
- The Con: It does not stop spam. Spammers are smart; they have scripts that automatically strip out everything between the + and the @ symbol, revealing your real email address. Use this for organization, not for security.
Establishing a Digital Hierarchy
To truly reduce spam, you need to structure your digital life into tiers. Do not treat all emails equally.
Tier 1: The Vault (Your Real Email)
This address is sacred. It is for your bank, your doctor, your family, and your employer. It is never typed into a random form. It is never used for shopping.
Tier 2: The Masked Manager (Aliases)
This is for services you trust but want to control. Netflix, Amazon, Spotify, your favorite newsletters. Use a forwarding service (like SimpleLogin) so you can cut the cord if necessary.
Tier 3: The Trash Can (Burner Emails)
This is for everything else. Free Wi-Fi, one-off downloads, sketchier websites. These addresses exist for minutes and then die.
Advanced Strategy: The Custom Domain Defense
If you want the ultimate level of control and professionalism, buy your own domain name (e.g., @yourname-mail.com) and connect it to a service like SimpleLogin or Proton Mail.
Why do this?
Some websites block known temporary email domains. If a website sees @10minutemail.com, it might reject the sign-up. However, if you have your own custom domain, they cannot distinguish it from a legitimate business address.
The “Catch-All” Method:
With a custom domain, you can invent addresses on the fly without even setting them up first. You can walk into a store called “Target” and tell the cashier your email is target@yourname-mail.com.
If you set up a “Catch-All” routing rule, that email will arrive in your inbox. If Target later sells your data, and you start getting spam at target@yourname-mail.com, you know exactly who betrayed you. You can then block that specific address.
The Risks: Are Temporary Emails Safe?
Privacy does not always equal security. When you use a temporary email service, you are trusting that service with the contents of the emails until they are forwarded or deleted.
- No Encryption: Most “throwaway” sites do not encrypt emails. The site administrators could technically read the incoming mail. Do not use them to receive sensitive data (passwords, private photos, confidential documents).
- Shared Domains: With throwaway services, once you release an address (e.g., user1@tempmail.com), it goes back into the pool. It is theoretically possible for someone else to get that same address later and receive mail intended for you. (Masking services like Apple and SimpleLogin avoid this by reserving the alias for you permanently).
The Rule of Thumb: Use a temporary email for junk transactions. Use encrypted, reputable email providers (like Proton or Gmail with Advanced Protection) for life transactions.
Digital Hygiene: Beyond the Burner Email
Temporary emails are just one pillar of a robust anti-spam strategy. To truly secure your inbox, you must combine it with other digital hygiene habits.
The “Unsubscribe” Trap
Be careful with the “Unsubscribe” button. On legitimate marketing emails (Target, Amazon), it works. On shady spam emails (generic Viagra ads, “You won an iPhone”), clicking unsubscribe confirms your email is active. It is safer to mark these as “Spam” or “Junk” so your provider’s filters learn to block them.
Disable Image Loading
Spammers embed tiny, invisible “tracking pixels” in emails. When you open the email and the images load, that pixel pings the spammer’s server, telling them: “He opened it at 10:00 AM, in New York, on an iPhone.”
Go to your email settings and select “Ask before displaying external images.” This stops the tracking and confirms you are a ghost.
Use a Secondary “Junk” Account
If you don’t want to use temporary services, create a permanent “Junk” Gmail or Yahoo account. Use this for loyalty programs, random app signups, and dating apps. Check it once a month. If it gets breached, your primary identity remains safe.
Troubleshooting Common Issues
Some of the common troubleshooting issues are below.
The Site Blocked My Burner Email:
Many websites are aware of temporary email domains and blacklist them. If you try to sign up and get an error saying “Please use a valid email address,” the site has blocked that specific domain (e.g., @10minutemail.com).
- The Fix: Use a different burner service, or better yet, use an aliasing service like SimpleLogin with a custom domain. Websites rarely block custom domains.
I Accidentally Closed the Tab:
If you used a true burner service and closed the tab before verifying, that account is gone. You will have to sign up again with a new burner email.
I Need to Reset a Password on an Old Account:
If you used a burner email for an account you now care about (e.g., an old gaming account) and you forgot the password, you are likely out of luck. The password reset link will be sent to an email address that no longer exists. This is why you must move accounts from Tier 3 (Burner) to Tier 2 (Alias) if they become important to you.
Conclusion
The battle against spam is an asymmetric war. Marketers have automation, AI, and billions of dollars. You have your attention and your privacy.
Using temporary email addresses is a way of leveling the playing field. It is a declaration that your personal data belongs to you, not to the algorithm. It allows you to access the utility of the internet—the discounts, the information, the connectivity—without the hangover of spam and the risk of data exposure.
Start today. The next time a website asks for your email address, pause. Ask yourself: “Does this site deserve my real identity?” If the answer is no, reach for a burner. Your future self, staring at a clean, organized, and secure inbox, will thank you.